Giving iOS Lockdown Mode Another Look
There was an interesting story this week in Wired about an unsettling development in the iPhone security world.
A sophisticated iPhone exploit framework known as “Coruna” appears to have originated from tools developed for US government use, before making its way through the murky exploit market. From there it seems to have ended up first in the hands of Russian espionage groups targeting Ukrainians, and later with cybercriminal operations stealing cryptocurrency from victims. The toolkit bundles multiple full iOS exploit chains and more than twenty individual exploits, capable of compromising vulnerable devices simply by visiting a malicious website.
What caught my eye, though, was a small but notable detail: the exploit kit apparently checks for Lockdown Mode and does not attempt infection if it’s enabled.
This isn’t the first time Lockdown Mode has stopped an attack dead in its tracks. When the FBI raided the home of Washington Post reporter Hannah Natanson earlier this year, court records show their forensics team couldn’t extract a thing from her iPhone. Lockdown Mode made the device a non-starter from the outset.
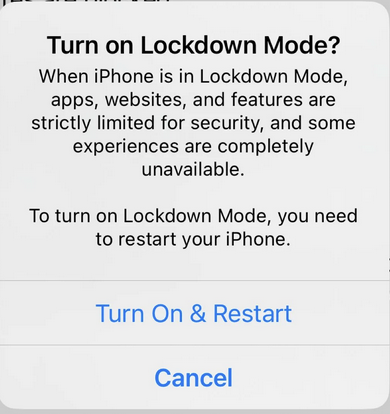
I tried Lockdown Mode when Apple first released it a few years back. At the time I left it on for a few days, but eventually turned it off. Some sites I rely on simply weren’t behaving properly, and it felt a bit too restrictive for everyday use.
Since then, though, Apple has gradually improved the feature’s usability, for example by allowing exceptions for trusted websites, while keeping the stronger security posture in place. Reading about real-world exploit chains like this finding their way from state actors to ordinary criminals was a good reminder that these defences aren’t purely theoretical.
For people like myself who tried Lockdown Mode early on and gave up, it may well be worth another look now that the rough edges have been smoothed out a bit.
For the full story, the Wired article is well worth a read.