SMS 2FA Will Die, But Not for the Reason You Think
The security community has long argued that SMS-based two-factor authentication is insecure. SIM swapping, SS7 interception, and social engineering are real and well documented.
But SMS 2FA is unlikely to disappear because of those attacks. It is becoming untenable because sending a single authentication text in the United States now requires navigating a bureaucratic system that small companies and independent developers struggle to clear.
A2P 10DLC
Under the A2P 10DLC framework, businesses must register before sending application-to-person SMS. That means registering a brand, registering a campaign, describing the use case, and waiting for approval from providers and carriers.
In theory, this reduces spam. In practice, it introduces fees, delays, and opaque review processes.
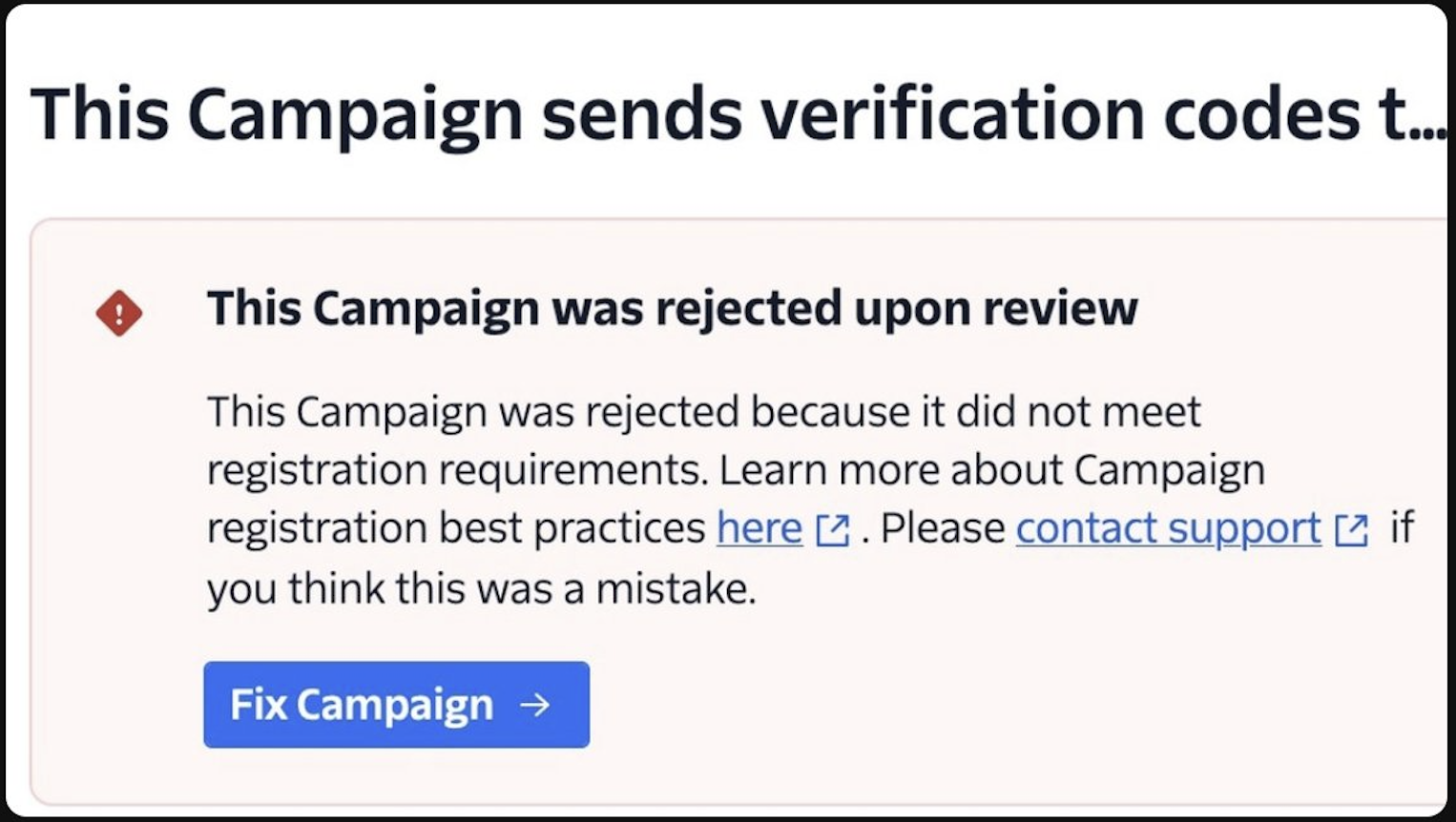
I spent over a week attempting to register a simple OTP-only application with two providers. The application does one thing: send six-digit authentication codes. It was rejected multiple times for vague or shifting procedural reasons. There is no fast path for a minimal, legitimate use case.
The issue is not that OTP over SMS is controversial. It is that the approval system is inconsistent and difficult to navigate.
The Economics
The 10DLC process adds monthly brand fees, campaign registration fees, and per-message surcharges. For large enterprises, these costs are minor. For small teams and side projects, they are meaningful.
The fee structure is layered and frequently updated. Calculating the true cost of sending a single OTP often requires reading multiple documentation pages or speaking to sales.
This shifts SMS from a simple utility into a gated service where compliance overhead and recurring fees discourage small senders. The system may reduce some abuse, but it also raises the barrier to entry for everyone else.
The Rejections
The use case in question is the most basic SMS flow on the internet: send a code, verify the code, complete authentication.
Yet repeated rejections cited insufficient detail, concerns about projected volume, or requests for documentation not mentioned in the initial application. The objections were procedural, not substantive. The system is not selectively filtering bad actors. It is filtering broadly.
What Replaces SMS
Meanwhile, the industry has been moving toward stronger alternatives: authenticator apps, push-based approvals, passkeys, WebAuthn, and FIDO2. These methods are more secure and more resistant to phishing.
Migration away from SMS was expected to happen because better technologies emerged. Instead, it is being accelerated by friction in the delivery infrastructure itself.
Developers who cannot reliably send SMS will switch. Many will adopt stronger options. Some may implement weaker fallbacks or skip a second factor altogether because the simplest path no longer runs through a phone number.
The Endgame
The 10DLC framework was introduced to combat A2P spam. Spam remains common. What has clearly increased is cost and complexity for legitimate senders.
The approval process is slow and inconsistent. Fees scale in ways that favor high-volume incumbents. Small developers face disproportionate friction for straightforward authentication use cases.
SMS 2FA is not failing primarily because of cryptographic weaknesses. It is failing because the surrounding regulatory and commercial structure has made it difficult to use.
It will not be remembered as the second factor that was too insecure. It will be remembered as the one that became too annoying to set up.